BlackBerry Persona & Machine Learning
Adaptive Security and AI to Protect Mobile Endpoints
BlackBerry Persona uses machine learning and predictive AI to dynamically adapt a security policy based on user location, device and other factors. By improving the user experience, it protects against human mistakes and well-intentioned workarounds.
Security that Travels and Adjusts with Your Users
What if your security policies could relax when your users are at the office or other trusted spaces, or change dynamically if they’re traveling in a higher-risk location? Or if those policies could sense when something is amiss and automatically lock down a device?
BlackBerry Persona enables a Zero Trust security environment, focused on earning trust across any endpoint and continuously validating that trust at every event or transaction.


Meet your highest security standards with BlackBerry Persona
- Dynamically adapts a security policy based on user geolocation, device, time, IP address and BlackBerry® Dynamics™ app identifiers.
- Decreases the risk that comes with lost devices
- Protects against device/app cloning and/or user impersonation

Continuous Authentication leverages passive biometrics and other usage-based patterns to continuously verify user identity in an unobtrusive fashion. A malicious user is automatically blocked from accessing apps when they exhibit anomalous behavior. This enhances the security posture and at the same time, improves the end user experience over having a static timeout.
BlackBerry Persona creates the best experience for end users while ensuring the best security and compliance posture.
- Streamlined access to apps and services without having to re-authenticate when in trusted locations
- Adapts security and policy posture to actual context, versus applying only static policies
- Enables “zero sign-in” and/or increasing timeouts if a user is in a low-risk pattern in high-trust location

BlackBerry Persona provides a contextual system for Unified Endpoint Management and protection.
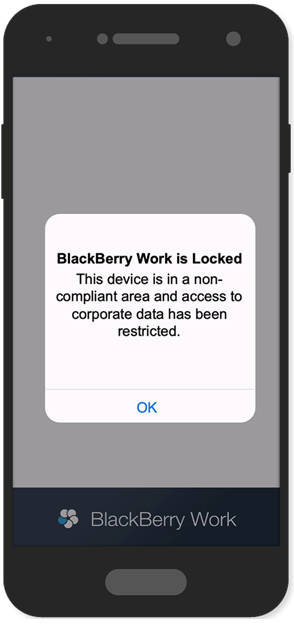
- Relaxes security policies when an end user is in a trusted location and dynamically adjusts when they travel to a higher-risk location
- Adapts device security to local regulatory requirements as an employee travels from one country to another
- Quarantines devices and apps before they can be used for malicious purposes
BlackBerry Persona allows the user experience design and security/policy posture to be mutually and dynamically optimized, versus in conflict.
- Determines what level of access should be granted to any device or application at any given moment
- Dynamically adapts security requirements for devices and applications without impacting performance
- Proactively detects anomalous behavior and prevents potentially malicious activity
.png)
BlackBerry Persona adds a layer of adaptive security to your existing UEM or UEM Cloud domain without introducing an additional software footprint.
- Builds on existing investments in BlackBerry UEM, BlackBerry Dynamics, and BlackBerry Enterprise Identity
- Can work with existing third-party infrastructure, like external IDPs (i.e. Ping, Okta, ADFS) or applications (i.e. Salesforce, Microsoft Office 365)
- Allows organizations to extend data, services and models with third-party threat detection systems
How it Works
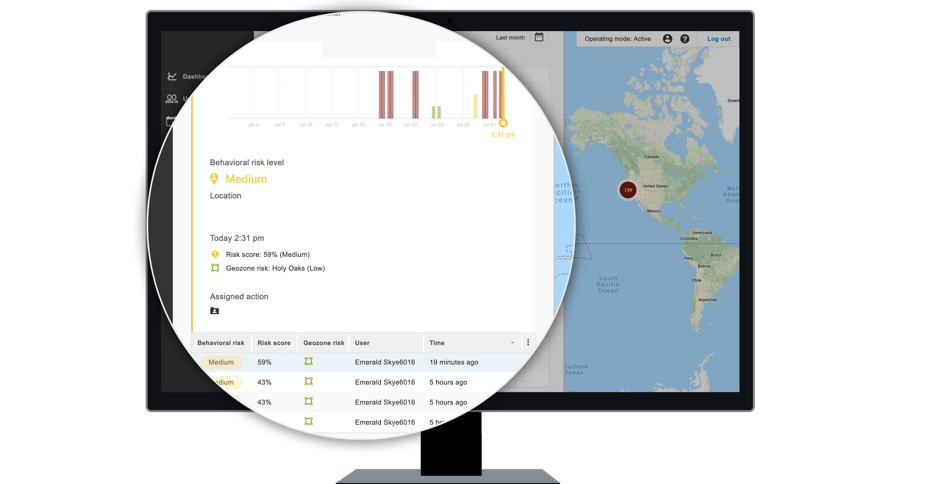
BlackBerry Persona, a part of the BlackBerry Spark platform, uses analytics-driven security to provide trust within Zero Trust environments. It adapts endpoint security policies based on situational risk:
BlackBerry Persona uses Machine Learning to identify behavioral and location patterns of multiple users to determine location-based risk. Known work locations can also be preloaded.
AI, combined with spatial data, determine a real-time risk score that adapts security policies for the user to create the best experience and security posture. It can:
- Grant access
- Adopt a policy
- Issue an authentication challenge
- Alert and remediate
Use Cases

Cloud Deployment for Connected Environments
Anne enters a retail branch
Anne is the regional manager for a major retail bank. With BlackBerry Persona, when she enters a retail branch, her presence is detected based on her mobile device’s geolocation. Her access to privileged apps appropriate for her role is automatically enabled upon her arrival. When she leaves, that access is disabled.

Hybrid Deployment for Unique Environments
Malicious hacker tries to access Salesforce app
Sally is an inside sales employee who primarily works from a corporate office. When BlackBerry Persona detects a combination of IP address, location and time that aren’t possible based on her last known access, it immediately denies access and takes remediating action to automate a logout, add the IP address to a watchlist and alert BlackBerry UEM of the high-risk event.

On-Premises Deployment for Closed Environments
Colonel Smith enters a restricted zone
Colonel Smith works at a government military base that has a restricted, high-security zone. With BlackBerry Persona, upon entering this zone, his camera and Bluetooth connection are disabled and access to restricted websites is enabled. When he leaves, camera and Bluetooth are enabled and restricted website access is disabled.
Copyright © 2025 All Rights Reserved by SolutionsPT.




